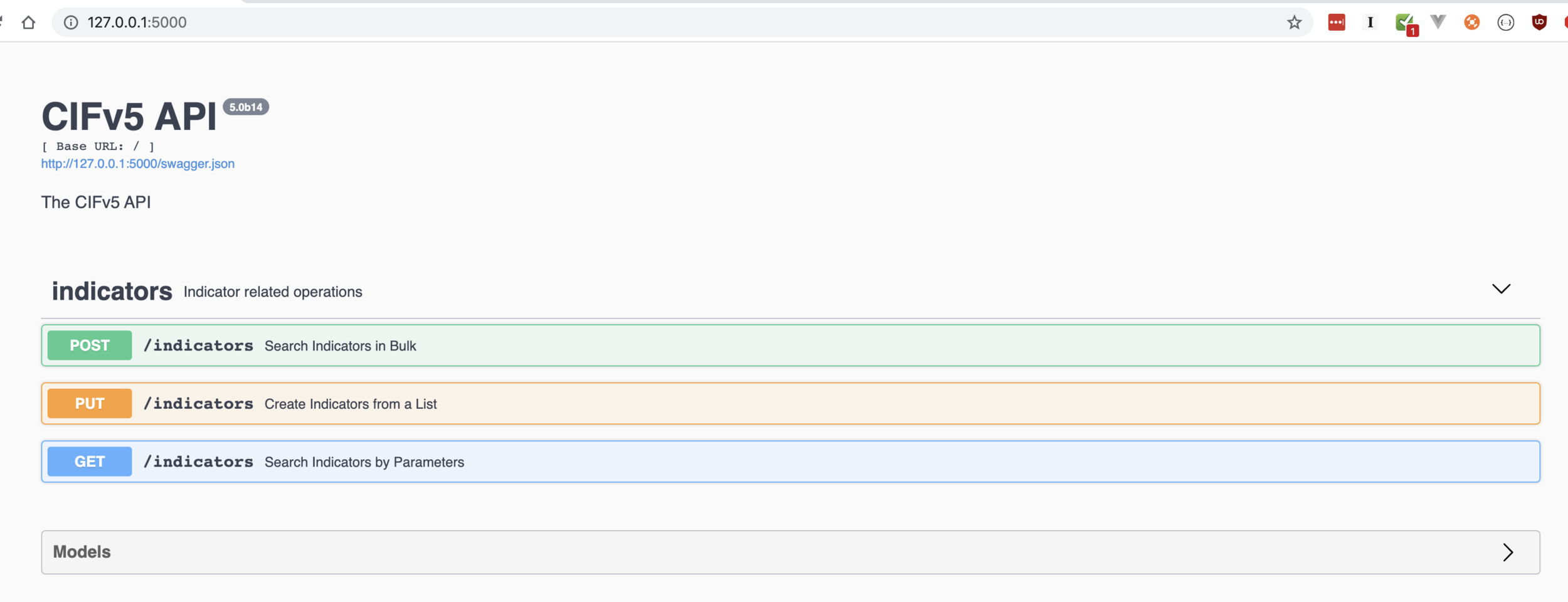
Test Driving CIFv5
Solve problems by writing doc first.
Solve problems by writing doc first.
The fastest way to threat intel is …
How to Brick your laptop- searching for ASN Information…
Not everyone can be Chuck Norris.
Sometimes- you can’t filter for…
Nothing hooks a zombie- like a brain on a stick.
You don’t need to deploy a full-blown threat intelligence platform, to hunt.





