Threat Hunting has become a very popular and loaded term in recent years. Depending on your role in this mess we call "the Internet"; the activity manifests in many different forms. As a network operator you might spend days wandering aimlessly through firewall logs. As a malware analyst your eyes might bleed from sandbox results on one screen and IDA on the other. As a forensics analyst it can mean days of pen-testing a new client environment, in search of something that may "bring down the company" or not be there at all.
(Of course that's just silly; we already know everyone has been hacked..)
From The Book of Knowledge:
“Threat hunting has traditionally been a manual process, in which a security analyst sifts through various data information using their own knowledge and familiarity with the network to create hypotheses about potential threats, such as, but not limited to, Lateral Movement by Threat Actors. To be even more effective and efficient, however, threat hunting can be partially automated, or machine-assisted, as well. In this case, the analyst uses software that leverages machine learning and user and entity behavior analytics (UEBA) to inform the analyst of potential risks.
The analyst then investigates these potential risks, tracking suspicious behavior in the network. Thus hunting is an iterative process, meaning that it must be continuously carried out in a loop, beginning with a hypothesis. The hypothesis can focus efforts on known exploits, potential bad actors or assets and data of value. Using security data, industry reports and other intelligence, the hypothesis is formed, and the hunt team sets out to prove or disprove its validity. Cyber threat hunts often employ both automated and manual tools and techniques to identify a compromise before it is detected.”
The past few years, vendor after vendor has pitched the "new shiny!" in an effort to capture this market. A new set of tools that will help you “find all the bad guys” and "win" in cyber. This feels akin to the various newsletters, hedge funds and trading techniques "guaranteed to make you a jillionaire". First off; if trading the markets were that easy and predictable- everyone would be rich. This doesn't mean the tools in and of themselves aren't useful- a hammer is useful, but it requires human application and precision to make it so.
Speaking as someone who makes over 10,000+ trades a year I can assure you, the market is random and it's really really hard to consistently make money. Not because the Market beats you- but because as humans it's hard to stay disciplined in your approach daily approach. It's the grind that separates the winners from the losers. Those who develop process, learn to keep their ego in check and stick with it; have a much higher probability of being successful. Those who get cocky, sloppy and trade too big, inevitably blow out.
In my opinion, "Threat Hunting" is much the same. There are some great ideas and tools that can help find all those needles in the needle-stack. However, without good process and discipline, adversaries will find your vulnerabilities and exploit them. As in trading; there is no silver bullet tool that will help you print money. It's the combination of tools and processes that will keep you ahead of your attackers. Like passive investing; passive security architectures have a high probability of LOSING YOU MONEY. That should make nothing but sense to most professionals. Where in life do you make MORE money by being passive in your environment?
Context
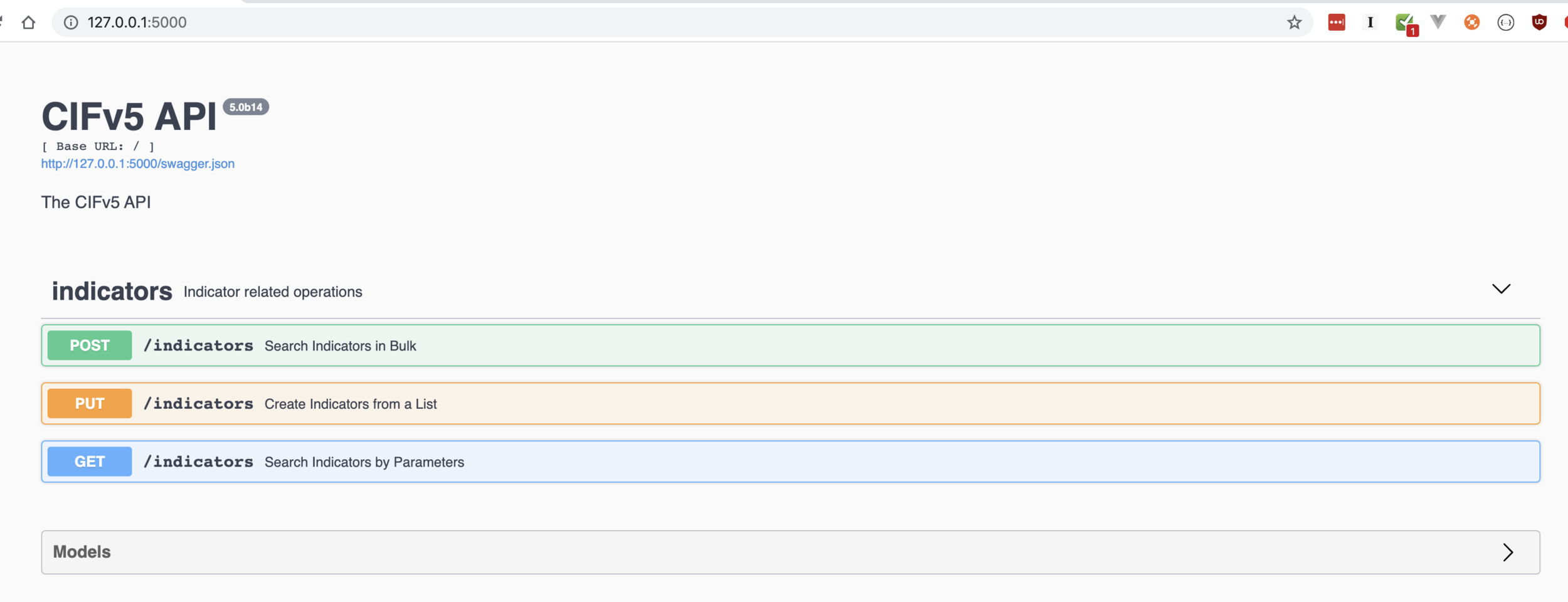
In my world- threat hunting is in understanding the context in which an IP is being used (or abused). When I first started writing CIF, the goal was gathering all the information I could with respect to network based indicators (IPs, URLs, FQDNs, etc) and SHOVE those IOCs into a firewall as quickly as possible. It quickly evolved into "hey- there's a lot of IP data we can search when we observe some odd network traffic". The problem was (is?) the process of investigating an IP address requires the entire CIF (or pick your favorite threat intel) platform to be configured and deployed. As SIMPLE as that has become- it’s not always feasible.
There are of course other ways of accomplishing this, including some really neat browser plugins that gives you "all the services". Most of which include us building out our own custom python toolkits that thread poorly and aren't extensible. As I've built CIF out over the years I've been just as culpable of this. The concept of automated "hunters" has always been built into the framework- but never in a way that enables others to build it into their own hunting services, shell scripts.
Not everyone wants to run a local CIF instance, but that doesn't mean they shouldn't be able to capture some of its insights, value and other lessons learned in their own hunting processes.