Test Driving CIFv5
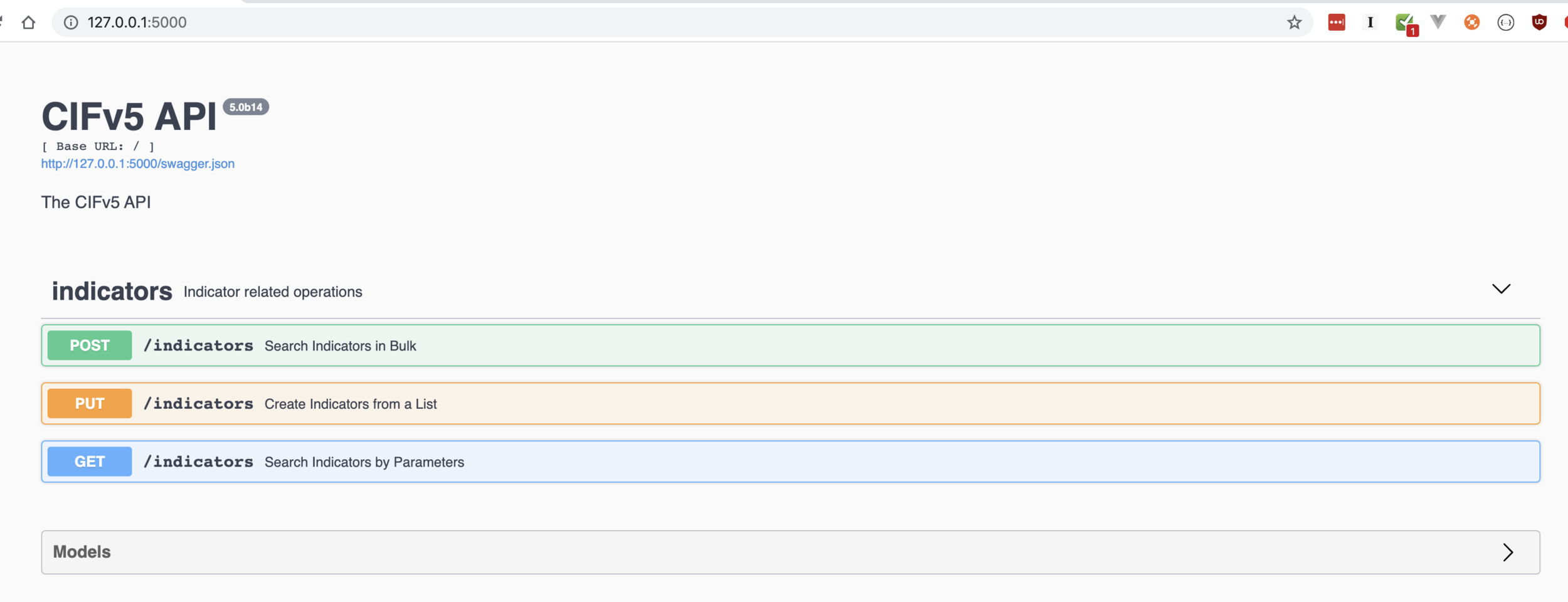
Solve problems by writing doc first.
Solve problems by writing doc first.
The fastest way to threat intel is …
Think about the problem you’re actually trying to solve- not the indicators themselves. Indicators for the sake of indicators is just plain…
Sometimes- you can’t filter for…
If you’re in opsec, you shouldn’t be writing SQL until…
Pretty soon, you find yourself back, staring at this "snort signatures" pattern problem. A small, elegant mathematical formula representing something your sensors should be detecting. All it's missing is a little normalization and a bit of an ever evolving data model behind it, representing the current state of the Internet…
What good is threat intel, if you have to spend time thinking about it?





