[FORECAST UPDATED] AI Agents as Regulated C2: Will Anyone Be Forced to Act?
![[FORECAST UPDATED] AI Agents as Regulated C2: Will Anyone Be Forced to Act?](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1772222784199-M36MYT1XN0BYL2OMOQ5Y/z.png)
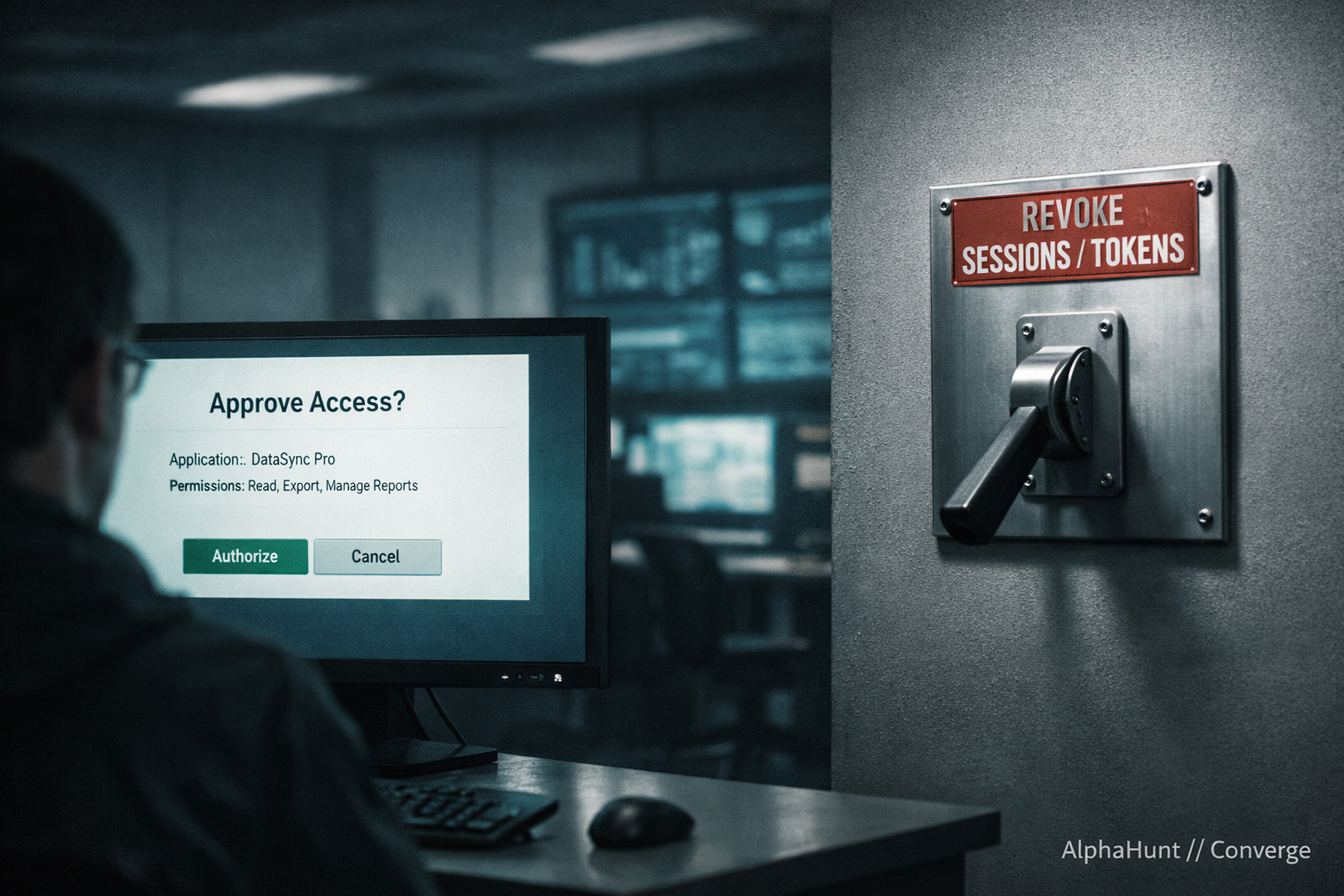
🤖🔒 AI agents = privileged integrations you can’t see. After GTG-1002 + vendors pushing agent access standards, the next shoe drops: do regulators/hyperscalers force default-on signed connectors + audit logs (aka “regulated C2”)?
![[FORECAST] Fortune 500s: Will Prompt Injection Trick IDE Agent Mode into Running Commands—or Leaking Secrets—by 2026?](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1771948879498-O4F3VJL57FKNFGOCPB4B/z.png)

![[FORECAST] Dismantled or Displaced? Cambodia’s Scam-Compound Crackdown by 2030?](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1771441636388-8CGD4O9428JFHZ4JIU2W/z.png)