The Next 3–6 Months: Where Threat Actors Will Move Faster Than Defenders
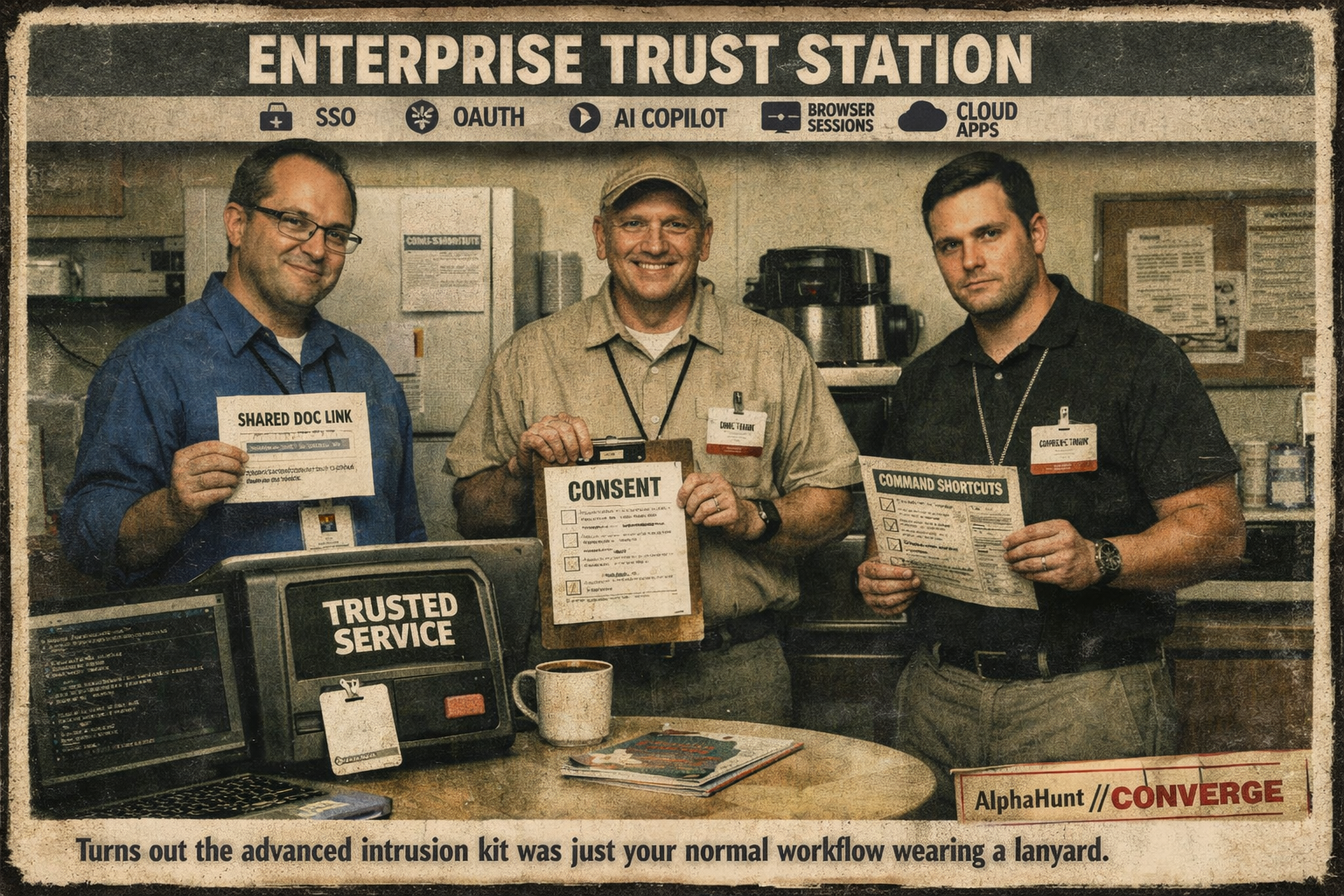
Everyone’s hunting “AI attacks.” Meanwhile the ugly money is still in trusted pages, stolen sessions, and users politely pasting the command for them.
Everyone’s hunting “AI attacks.” Meanwhile the ugly money is still in trusted pages, stolen sessions, and users politely pasting the command for them.
Three intrusion sets already excel at getting users to approve tools and auth flows. This assessment is probabilistic: it highlights who is best positioned to adapt that tradecraft to MCP-style environments next..
![[DEEP RESEARCH] Who’s Most Likely to Abuse MCP Integrations? UNC3944, TraderTraitor, UNC6293](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1772554580184-FFRX326MRDC0Y49QBKE4/z.png)