FINAL FORECAST: A No forecast can still mean ugly OT cleanup
The forecast likely resolves No, but the useful lesson is where Iran-linked operators still depend on access defenders can pressure.
The forecast likely resolves No, but the useful lesson is where Iran-linked operators still depend on access defenders can pressure.
The forecast is stubborn.
Iran-linked PLC activity is real. The harder part is proof: numbers, attribution, novelty.
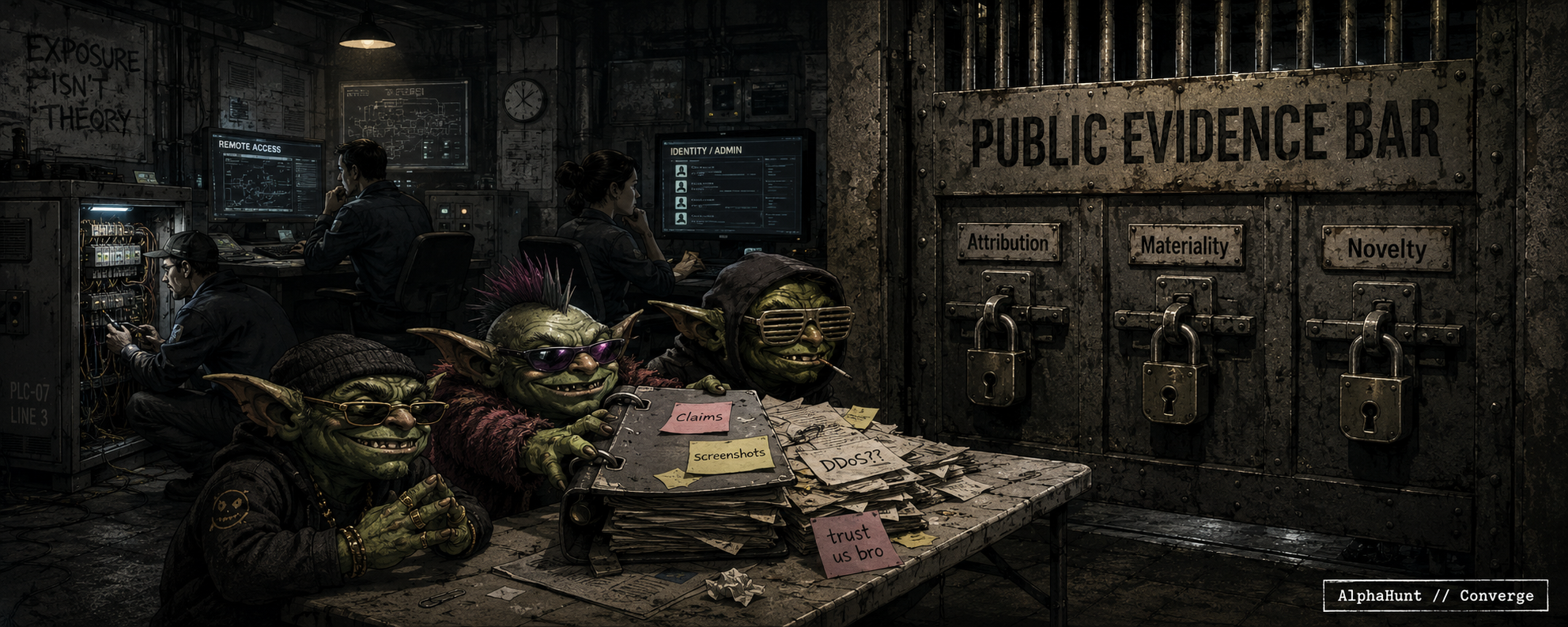
Noise is not qualification.
Iran-linked cyber activity is not the part defenders should hand-wave.
The part to distrust is the scoreboard.
Every nuisance claim wants to dress up as “critical infrastructure impact.” The evidence bar still matters.
The industry loves a neat PLC story because it keeps the threat in a box you can point at.
The less fun version is when the same campaign walks through identity or an admin plane your org still treats like plumbing.
Everyone saw the PLC headline and immediately built their whole Iran take around exposed controllers. Cool. The nastier question is what happens when the next move comes through identity, admin planes, or some target class nobody staffed for.
Iran cyber risk is not about whether they’ll be active. They will. The real question is whether the next 8 weeks produce a publicly attributed, materially disruptive hit with a new twist beyond the usual password-spray sludge. Tenant sabotage is the part to watch. 👀🔥
Iran cyber risk isn’t just “watch for wipers.” It’s the same ugly identity-first playbook: password sprays, MFA abuse, cloud access… then maybe admin-plane sabotage. Recent reporting says activity is already reaching U.S. targets. Cute. 🚨🔐🧨
![[FORECAST] Iran Cyber Is Active. The Evidence Bar Is Harder.](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1778696857364-AVRHX3XKXJ0MP943CHJA/zz.png)
![[FORECAST ] Iran’s Cyber Window Is Still Open—But the Qualification Clock Is Now the Hardest Adversary (Updated 2026-05-05!)](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1777919075902-TL4QPYZKLJGOXEET30IY/z.png)
![[FORECAST] Iran’s Cyber Window Stays Open—But the Novelty Bar Is Tougher Now (Updated: 2026-04-23)](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1776885867045-0KK8LC3Y5O50IO9SPNTG/z.png)
![[FORECAST] Beyond PLCs: Are Iran-Linked Operators More Likely to Chase New Targets, New Tooling, or New Impact? UPDATED 2026-04-08!](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1775677258908-F0SXWFIDAWO0IXFL7E4S/z.png)
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs - UPDATED: 2026-03-26](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1774465668081-824GFNW77DFJR8LFPZ9F/z.png)
![[FORECASTS] From Password Sprays to Tenant Sabotage: The 8-Week Iran Cyber Risk for U.S. and Israeli Orgs](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1773672177786-ETLYZK0QIPMLI49ANREA/z.png)