The Real Government Fraud Story- Identity Infrastructure
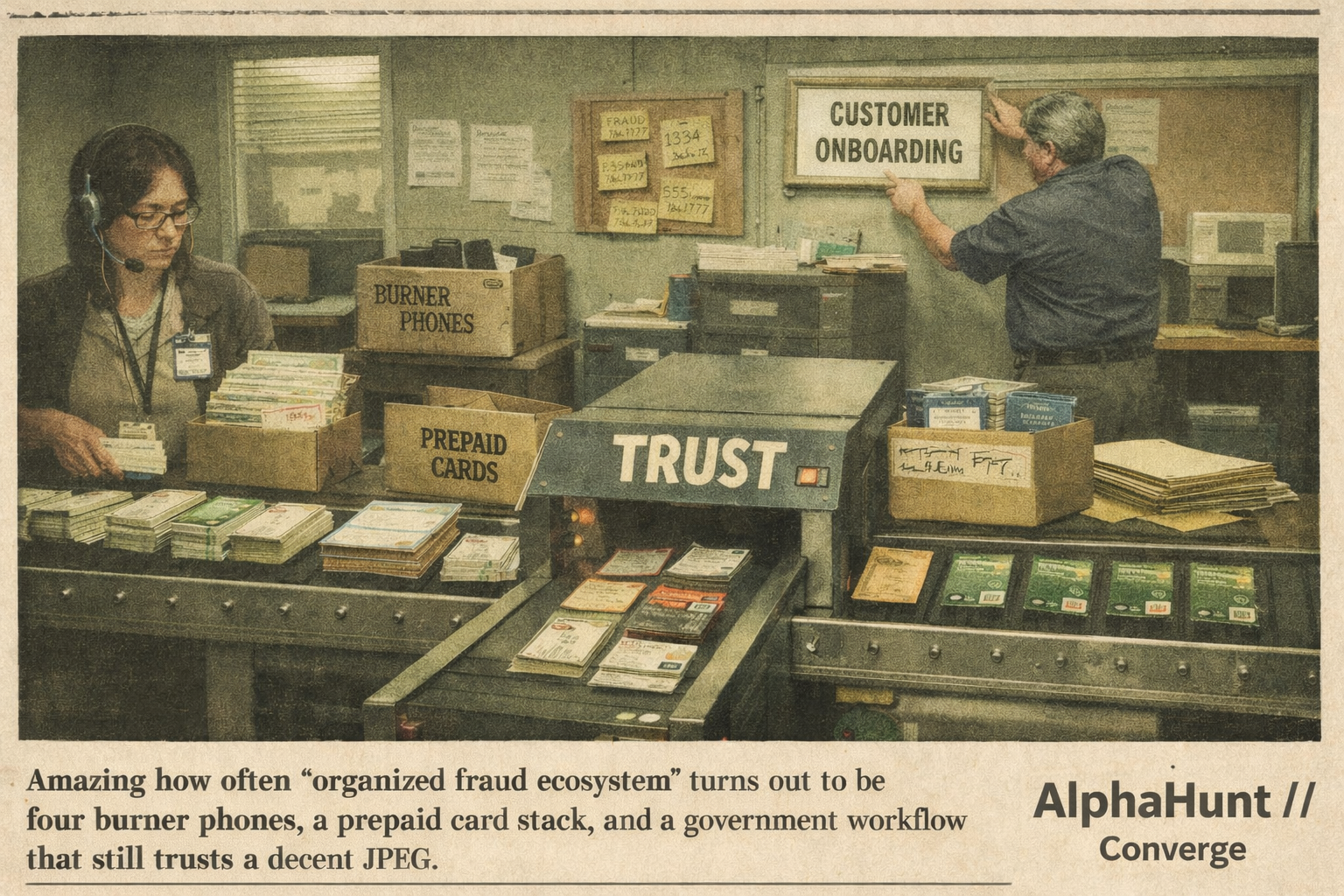
“Fraud” makes it sound random. It isn’t. It’s identity infrastructure with a cash-out layer. Same proofing gaps, same rails, same reusable parts. People keep chasing claims instead of the production line.
