[FORECAST] The Fake Hire Was Never Just an HR Problem
![[FORECAST] The Fake Hire Was Never Just an HR Problem](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1780937063155-3MZXBY4AZUR2DZIMPZC5/z.png)
The fake remote IT worker story gets talked about like hiring fraud, sanctions exposure, or payroll diversion.
The fake remote IT worker story gets talked about like hiring fraud, sanctions exposure, or payroll diversion.
AI coding tools are becoming trusted middlemen. That gives defenders a new attack path to understand before it gets ugly.
The forecast likely resolves No, but the useful lesson is where Iran-linked operators still depend on access defenders can pressure.
The forecast is stubborn.
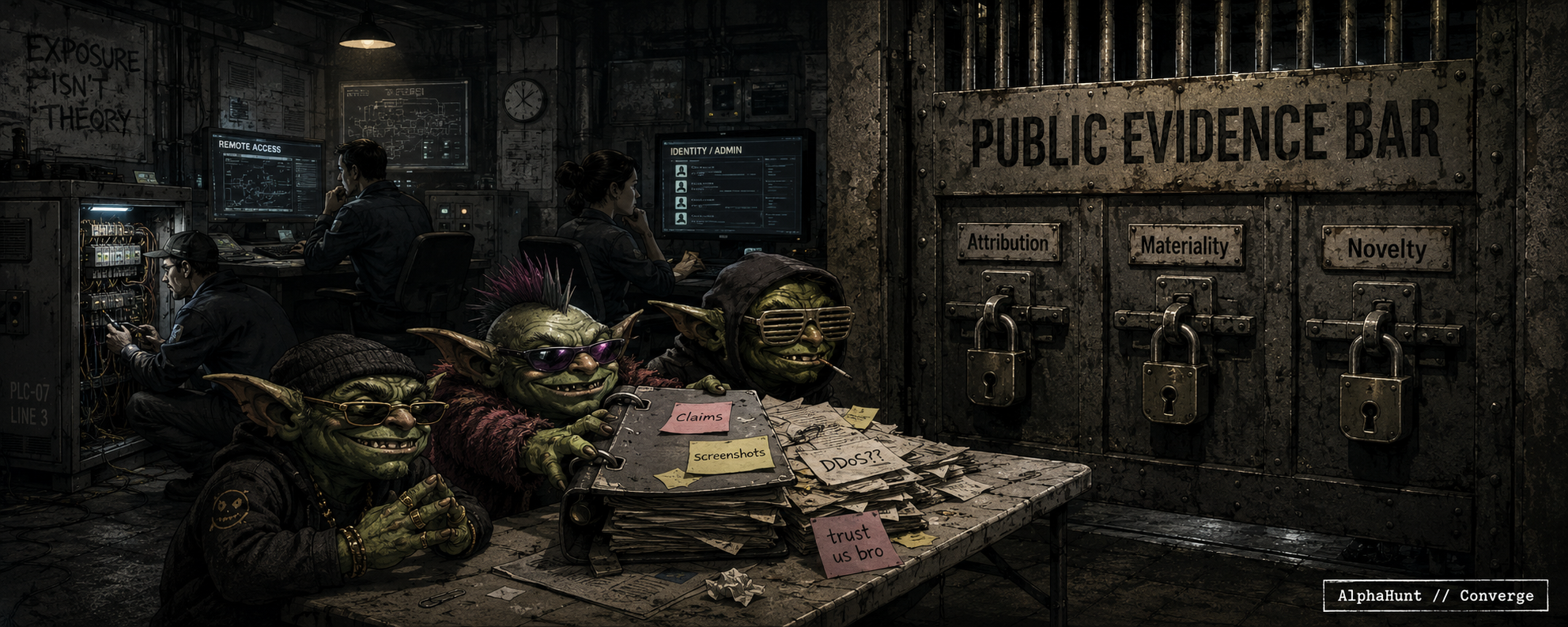
Iran-linked PLC activity is real. The harder part is proof: numbers, attribution, novelty.
Noise is not qualification.
We’re revising the Akira hospital disruption forecast down to 2%. The risk is real, but the question is narrower than it looks.
“Secure by default” sounds great until it meets BYOD, VDI, federated SSO, and the help desk exception list from hell.
Device-bound sessions help.
Waiting for every SaaS vendor to flip the default is not a strategy.
Iran-linked cyber activity is not the part defenders should hand-wave.
The part to distrust is the scoreboard.
Every nuisance claim wants to dress up as “critical infrastructure impact.” The evidence bar still matters.
![[FORECAST] AI coding tools are becoming a new secret path](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1780161447430-HJP9Q2NO18H02UK10367/z.png)
![[FORECAST] Iran Cyber Is Active. The Evidence Bar Is Harder.](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1778696857364-AVRHX3XKXJ0MP943CHJA/zz.png)
![[FORECAST] Will Akira trigger a week-long hospital disruption by end of 2026? (Updated 2026-05-11)](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1778531572870-0NAMW0NJCH4SU18GKYMM/z.png)
![[FORECAST] Device-Bound Sessions Are Coming. Defaults Are the Hard Part.](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1778085280152-5T15KO073L1XKEUK2WU9/z.png)
![[FORECAST ] Iran’s Cyber Window Is Still Open—But the Qualification Clock Is Now the Hardest Adversary (Updated 2026-05-05!)](https://images.squarespace-cdn.com/content/v1/54bd1221e4b05e8a3646d021/1777919075902-TL4QPYZKLJGOXEET30IY/z.png)